★★★2 lets encrypt 인증서 acme.sh 시놀로지 자동 업데이트 만들기 ★★★
첨부
등록일
2024.07.10 13:00
컨텐츠 정보
- 8,250 조회
- 6 댓글
- 0 추천
-
목록
본문
★★★2 lets encrypt 인증서 acme.sh 시놀로지 자동 업데이트 만들기 ★★★
★★★ lets encrypt 인증서 재설치 acme.sh 시놀로지 멀티 인증서 만들기 ★★★
https://11q.kr/www/bbs/board.php?bo_table=s11&wr_id=12740
이어
자동 데이트 입니다
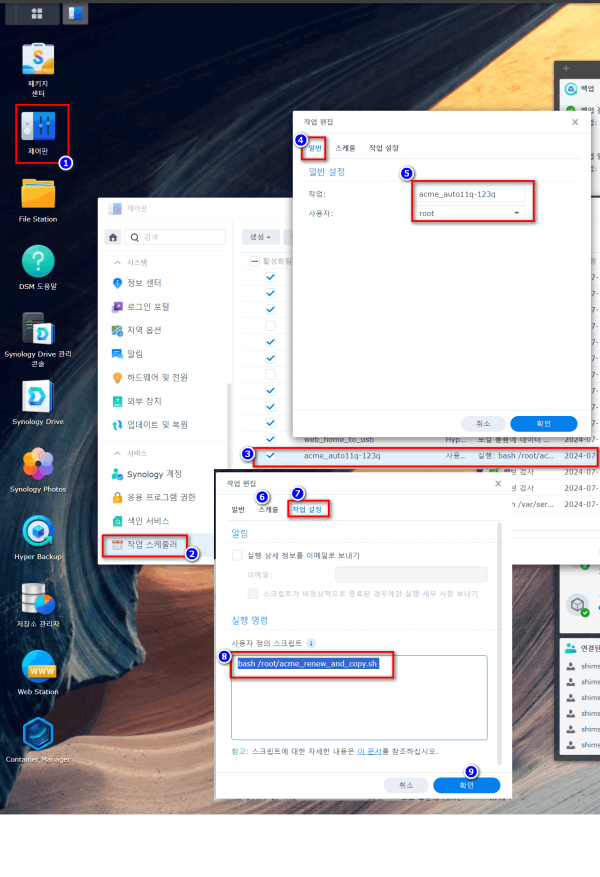
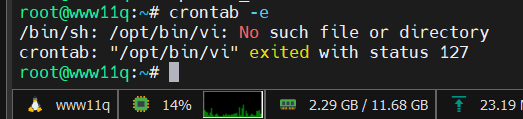
crontab 이 재부팅후 동작하지 않아 dsm에서 작업스케줄러로 구성 합니다
작업스케줄러로 구성
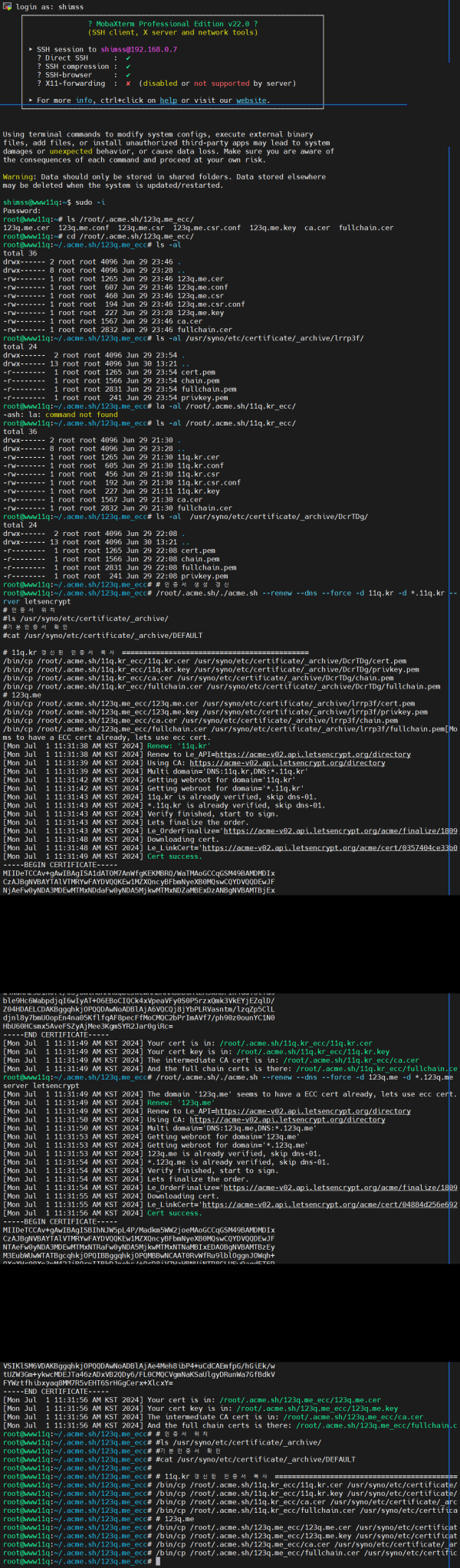
1주일후 업데이트 .>> 테스트 >>> ssh 터미널로 생성 확인 작업
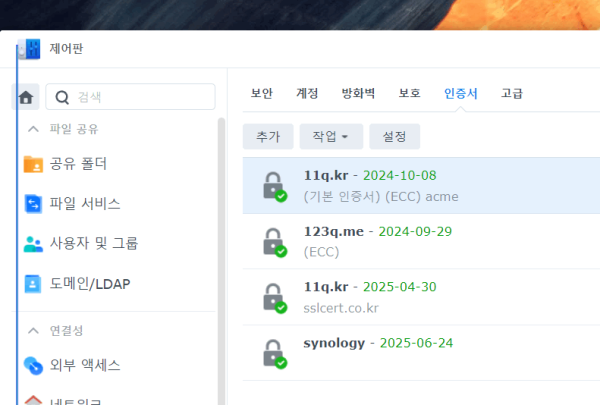
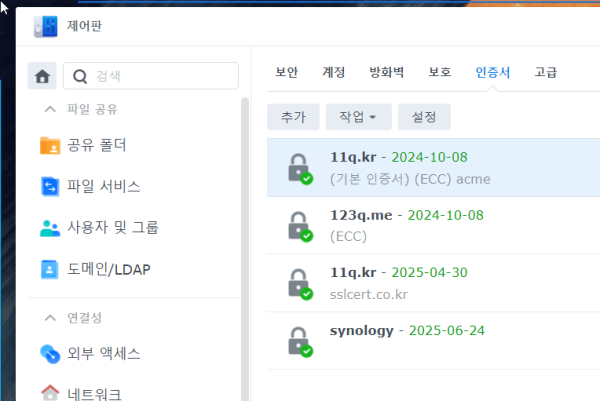
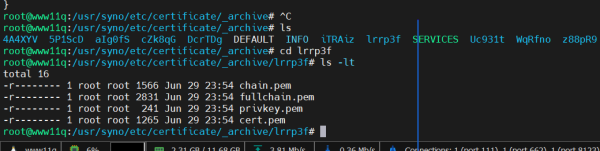
1개 먼저 인증서 생성(11Q.KR) ,,,123q.me인증서 생성 확인 (저는 2개의 도메인을 사용중)
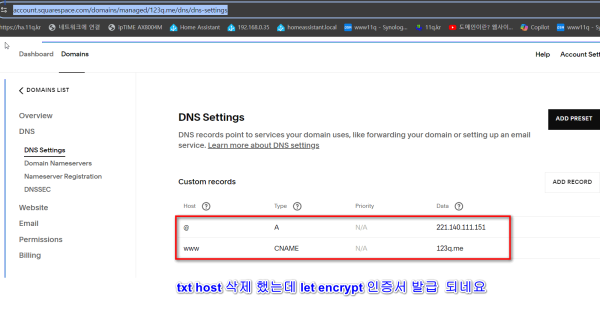
123Q.ME 인증서 생성
DSM 재부팅후
crontab -e
내일 실행 도는 일주일 후 인증서 날짜 확인 합니다,
<작업 내용>
주어진 명령어들을 매주 1회 자동으로 실행되도록 crontab을 설정하는 방법을 설명드리겠습니다.
자동 데이트
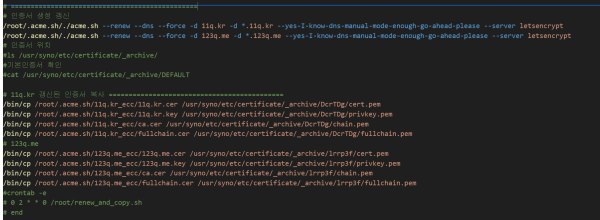
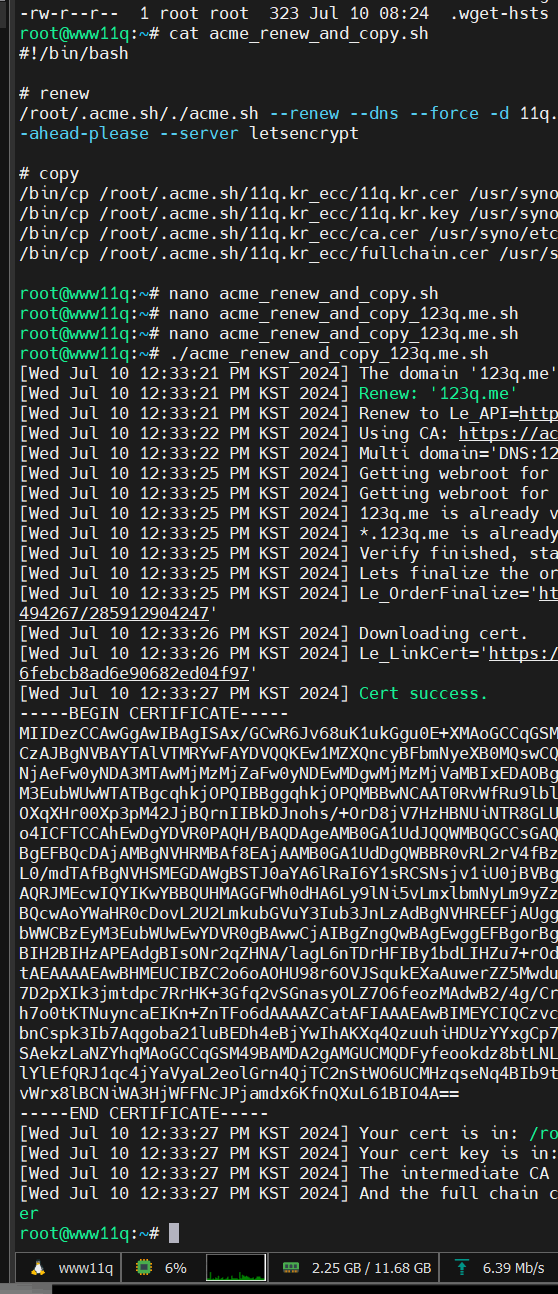
cat acme_renew_and_copy.sh 작성
chmod a+x acme_renew_and_copy.sh
nano acme_renew_and_copy.sh
#!/bin/bash
# nano acme_renew_and_copy.sh 작성
# acme.sh install
#opkg update
#opkg install nano
#opkg install cron
#/opt/etc/init.d/S10cron start
#ln -s /opt/etc/init.d/S10cron /opt/etc/init.d/S99cron
#export VISUAL=nano crontab -e
# */5 * * * * echo "cron test: $(date)" >> /tmp/test.txt
#cat /tmp/test.txt
#wget -O - https://get.acme.sh | sh
# txt 값생성
#/root/.acme.sh/acme.sh --issue --dns --force -d 11q.kr -d *.11q.kr --yes-I-know-dns-manual-mode-enough-go-ahead-please --server letsencrypt
# /root/.acme.sh/acme.sh --issue --dns --force -d 123q.me -d *.123q.me --yes-I-know-dns-manual-mode-enough-go-ahead-please --server letsencrypt
#ssh txt 적용 확인
#nslookup
#> set type=txt
#> _acme-challenge.11q.kr
# ===============================================
# 인증서 생성 갱신
/root/.acme.sh/./acme.sh --renew --dns --force -d 11q.kr -d *.11q.kr --yes-I-know-dns-manual-mode-enough-go-ahead-please --server letsencrypt
/root/.acme.sh/./acme.sh --renew --dns --force -d 123q.me -d *.123q.me --yes-I-know-dns-manual-mode-enough-go-ahead-please --server letsencrypt
# 인증서 위치
#ls /usr/syno/etc/certificate/_archive/
#기본인증서 확인
#cat /usr/syno/etc/certificate/_archive/DEFAULT
# 11q.kr 갱신된 인증서 복사 ============================================
/bin/cp /root/.acme.sh/11q.kr_ecc/11q.kr.cer /usr/syno/etc/certificate/_archive/DcrTDg/cert.pem
/bin/cp /root/.acme.sh/11q.kr_ecc/11q.kr.key /usr/syno/etc/certificate/_archive/DcrTDg/privkey.pem
/bin/cp /root/.acme.sh/11q.kr_ecc/ca.cer /usr/syno/etc/certificate/_archive/DcrTDg/chain.pem
/bin/cp /root/.acme.sh/11q.kr_ecc/fullchain.cer /usr/syno/etc/certificate/_archive/DcrTDg/fullchain.pem
# 123q.me
/bin/cp /root/.acme.sh/123q.me_ecc/123q.me.cer /usr/syno/etc/certificate/_archive/lrrp3f/cert.pem
/bin/cp /root/.acme.sh/123q.me_ecc/123q.me.key /usr/syno/etc/certificate/_archive/lrrp3f/privkey.pem
/bin/cp /root/.acme.sh/123q.me_ecc/ca.cer /usr/syno/etc/certificate/_archive/lrrp3f/chain.pem
/bin/cp /root/.acme.sh/123q.me_ecc/fullchain.cer /usr/syno/etc/certificate/_archive/lrrp3f/fullchain.pem
#crontab -e
# 0 2 * * 0 /root/renew_and_copy.sh
# end
123Q.ME는 lrrp3f 로 설정
자동화 적용 > 자동 데이트
crontab -e
# (/tmp/crontab.XXXX8PaLqt installed on Sat Jun 29 17:56:01 2024)
# (Cron version V5.0 -- $Id: crontab.c,v 1.12 2004/01/23 18:56:42 vixie Exp $)
# */5 * * * * echo "cron test: $(date)" >> /tmp/test.txt
9 10 * * * "/root/.acme.sh"/acme.sh --cron --home "/root/.acme.sh" > /dev/null
0 2 * * 0 /root/renew_and_copy.sh
============================================
인증서 2일후 재발급 테스트
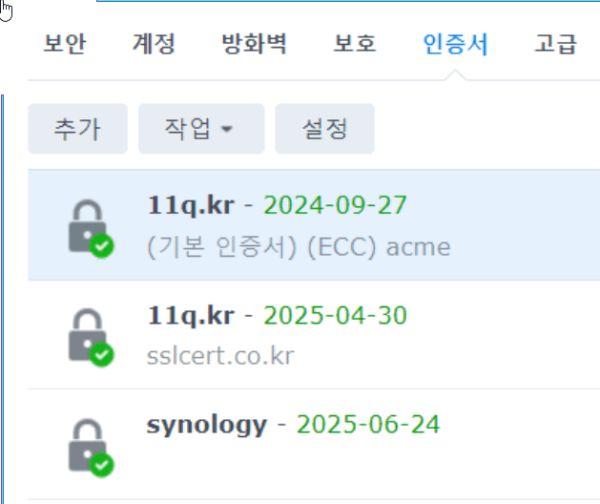
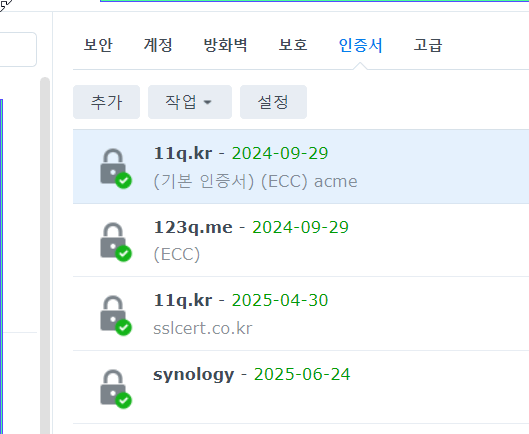
자동 업데이트 확인 9/27
123q 까지
2일후 생성 화인 > 9/27 ===> 9/29 로 변경
☞ https://11q.kr 에 등록된 자료 입니다. ♠ 정보찾아 공유 드리며 출처는 링크 참조 바랍니다♠
관련자료
-
첨부등록일 2024.07.10 13:00
댓글 6
11qkr님의 댓글
#!/bin/bash
# nano acme_renew_and_copy.sh 작성
# acme.sh install
#opkg update
#opkg install nano
#opkg install cron
#/opt/etc/init.d/S10cron start
#ln -s /opt/etc/init.d/S10cron /opt/etc/init.d/S99cron
#export VISUAL=nano crontab -e
# */5 * * * * echo "cron test: $(date)" >> /tmp/test.txt
#cat /tmp/test.txt
#wget -O - https://get.acme.sh | sh
# txt 값생성
#/root/.acme.sh/acme.sh --issue --dns --force -d 11q.kr -d *.11q.kr --yes-I-know-dns-manual-mode-enough-go-ahead-please --server letsencrypt
# /root/.acme.sh/acme.sh --issue --dns --force -d 123q.me -d *.123q.me --yes-I-know-dns-manual-mode-enough-go-ahead-please --server letsencrypt
#ssh txt 적용 확인
#nslookup
#> set type=txt
#> _acme-challenge.11q.kr
# ===============================================
# 인증서 생성 갱신
/root/.acme.sh/./acme.sh --renew --dns --force -d 11q.kr -d *.11q.kr --yes-I-know-dns-manual-mode-enough-go-ahead-please --server letsencrypt
/root/.acme.sh/./acme.sh --renew --dns --force -d 123q.me -d *.123q.me --yes-I-know-dns-manual-mode-enough-go-ahead-please --server letsencrypt
# 인증서 위치
#ls /usr/syno/etc/certificate/_archive/
#기본인증서 확인
#cat /usr/syno/etc/certificate/_archive/DEFAULT
# 11q.kr 갱신된 인증서 복사 ============================================
/bin/cp /root/.acme.sh/11q.kr_ecc/11q.kr.cer /usr/syno/etc/certificate/_archive/DcrTDg/cert.pem
/bin/cp /root/.acme.sh/11q.kr_ecc/11q.kr.key /usr/syno/etc/certificate/_archive/DcrTDg/privkey.pem
/bin/cp /root/.acme.sh/11q.kr_ecc/ca.cer /usr/syno/etc/certificate/_archive/DcrTDg/chain.pem
/bin/cp /root/.acme.sh/11q.kr_ecc/fullchain.cer /usr/syno/etc/certificate/_archive/DcrTDg/fullchain.pem
# 123q.me
/bin/cp /root/.acme.sh/123q.me_ecc/123q.me.cer /usr/syno/etc/certificate/_archive/lrrp3f/cert.pem
/bin/cp /root/.acme.sh/123q.me_ecc/123q.me.key /usr/syno/etc/certificate/_archive/lrrp3f/privkey.pem
/bin/cp /root/.acme.sh/123q.me_ecc/ca.cer /usr/syno/etc/certificate/_archive/lrrp3f/chain.pem
/bin/cp /root/.acme.sh/123q.me_ecc/fullchain.cer /usr/syno/etc/certificate/_archive/lrrp3f/fullchain.pem
# 자동업데이트
# crontab -e
# 0 2 * * 0 /root/renew_and_copy.sh
# end
# nano acme_renew_and_copy.sh 작성
# acme.sh install
#opkg update
#opkg install nano
#opkg install cron
#/opt/etc/init.d/S10cron start
#ln -s /opt/etc/init.d/S10cron /opt/etc/init.d/S99cron
#export VISUAL=nano crontab -e
# */5 * * * * echo "cron test: $(date)" >> /tmp/test.txt
#cat /tmp/test.txt
#wget -O - https://get.acme.sh | sh
# txt 값생성
#/root/.acme.sh/acme.sh --issue --dns --force -d 11q.kr -d *.11q.kr --yes-I-know-dns-manual-mode-enough-go-ahead-please --server letsencrypt
# /root/.acme.sh/acme.sh --issue --dns --force -d 123q.me -d *.123q.me --yes-I-know-dns-manual-mode-enough-go-ahead-please --server letsencrypt
#ssh txt 적용 확인
#nslookup
#> set type=txt
#> _acme-challenge.11q.kr
# ===============================================
# 인증서 생성 갱신
/root/.acme.sh/./acme.sh --renew --dns --force -d 11q.kr -d *.11q.kr --yes-I-know-dns-manual-mode-enough-go-ahead-please --server letsencrypt
/root/.acme.sh/./acme.sh --renew --dns --force -d 123q.me -d *.123q.me --yes-I-know-dns-manual-mode-enough-go-ahead-please --server letsencrypt
# 인증서 위치
#ls /usr/syno/etc/certificate/_archive/
#기본인증서 확인
#cat /usr/syno/etc/certificate/_archive/DEFAULT
# 11q.kr 갱신된 인증서 복사 ============================================
/bin/cp /root/.acme.sh/11q.kr_ecc/11q.kr.cer /usr/syno/etc/certificate/_archive/DcrTDg/cert.pem
/bin/cp /root/.acme.sh/11q.kr_ecc/11q.kr.key /usr/syno/etc/certificate/_archive/DcrTDg/privkey.pem
/bin/cp /root/.acme.sh/11q.kr_ecc/ca.cer /usr/syno/etc/certificate/_archive/DcrTDg/chain.pem
/bin/cp /root/.acme.sh/11q.kr_ecc/fullchain.cer /usr/syno/etc/certificate/_archive/DcrTDg/fullchain.pem
# 123q.me
/bin/cp /root/.acme.sh/123q.me_ecc/123q.me.cer /usr/syno/etc/certificate/_archive/lrrp3f/cert.pem
/bin/cp /root/.acme.sh/123q.me_ecc/123q.me.key /usr/syno/etc/certificate/_archive/lrrp3f/privkey.pem
/bin/cp /root/.acme.sh/123q.me_ecc/ca.cer /usr/syno/etc/certificate/_archive/lrrp3f/chain.pem
/bin/cp /root/.acme.sh/123q.me_ecc/fullchain.cer /usr/syno/etc/certificate/_archive/lrrp3f/fullchain.pem
# 자동업데이트
# crontab -e
# 0 2 * * 0 /root/renew_and_copy.sh
# end
11qkr님의 댓글
# 인증서 생성 갱신
/root/.acme.sh/./acme.sh --renew --dns --force -d 11q.kr -d *.11q.kr --yes-I-know-dns-manual-mode-enough-go-ahead-please --server letsencrypt
/root/.acme.sh/./acme.sh --renew --dns --force -d 123q.me -d *.123q.me --yes-I-know-dns-manual-mode-enough-go-ahead-please --server letsencrypt
# 인증서 위치
#ls /usr/syno/etc/certificate/_archive/
#기본인증서 확인
#cat /usr/syno/etc/certificate/_archive/DEFAULT
# 11q.kr 갱신된 인증서 복사 ============================================
/bin/cp /root/.acme.sh/11q.kr_ecc/11q.kr.cer /usr/syno/etc/certificate/_archive/DcrTDg/cert.pem
/bin/cp /root/.acme.sh/11q.kr_ecc/11q.kr.key /usr/syno/etc/certificate/_archive/DcrTDg/privkey.pem
/bin/cp /root/.acme.sh/11q.kr_ecc/ca.cer /usr/syno/etc/certificate/_archive/DcrTDg/chain.pem
/bin/cp /root/.acme.sh/11q.kr_ecc/fullchain.cer /usr/syno/etc/certificate/_archive/DcrTDg/fullchain.pem
# 123q.me
/bin/cp /root/.acme.sh/123q.me_ecc/123q.me.cer /usr/syno/etc/certificate/_archive/lrrp3f/cert.pem
/bin/cp /root/.acme.sh/123q.me_ecc/123q.me.key /usr/syno/etc/certificate/_archive/lrrp3f/privkey.pem
/bin/cp /root/.acme.sh/123q.me_ecc/ca.cer /usr/syno/etc/certificate/_archive/lrrp3f/chain.pem
/bin/cp /root/.acme.sh/123q.me_ecc/fullchain.cer /usr/syno/etc/certificate/_archive/lrrp3f/fullchain.pem
#crontab -e
# 0 2 * * 0 /root/renew_and_copy.sh
# end
/root/.acme.sh/./acme.sh --renew --dns --force -d 11q.kr -d *.11q.kr --yes-I-know-dns-manual-mode-enough-go-ahead-please --server letsencrypt
/root/.acme.sh/./acme.sh --renew --dns --force -d 123q.me -d *.123q.me --yes-I-know-dns-manual-mode-enough-go-ahead-please --server letsencrypt
# 인증서 위치
#ls /usr/syno/etc/certificate/_archive/
#기본인증서 확인
#cat /usr/syno/etc/certificate/_archive/DEFAULT
# 11q.kr 갱신된 인증서 복사 ============================================
/bin/cp /root/.acme.sh/11q.kr_ecc/11q.kr.cer /usr/syno/etc/certificate/_archive/DcrTDg/cert.pem
/bin/cp /root/.acme.sh/11q.kr_ecc/11q.kr.key /usr/syno/etc/certificate/_archive/DcrTDg/privkey.pem
/bin/cp /root/.acme.sh/11q.kr_ecc/ca.cer /usr/syno/etc/certificate/_archive/DcrTDg/chain.pem
/bin/cp /root/.acme.sh/11q.kr_ecc/fullchain.cer /usr/syno/etc/certificate/_archive/DcrTDg/fullchain.pem
# 123q.me
/bin/cp /root/.acme.sh/123q.me_ecc/123q.me.cer /usr/syno/etc/certificate/_archive/lrrp3f/cert.pem
/bin/cp /root/.acme.sh/123q.me_ecc/123q.me.key /usr/syno/etc/certificate/_archive/lrrp3f/privkey.pem
/bin/cp /root/.acme.sh/123q.me_ecc/ca.cer /usr/syno/etc/certificate/_archive/lrrp3f/chain.pem
/bin/cp /root/.acme.sh/123q.me_ecc/fullchain.cer /usr/syno/etc/certificate/_archive/lrrp3f/fullchain.pem
#crontab -e
# 0 2 * * 0 /root/renew_and_copy.sh
# end